Mass Adoption of Digital Ownership and Progressive Self Custody
Learn about how Account Abstraction (AA) and Multiparty Computation (MPC) can be used to onboard the next billion users into Web3.

Introduction
The potential for digital ownership to positively impact society by empowering individuals is vast. There are a number of important considerations on the road to mass adoption, including ease of use and the level of ownership an individual has over their digital goods. In other words, an individuals’ ability to resist theft, rugging, and censorship.
The aim of this article is to explore the methods that can be used to give each person a polished, convenient, and seamless way to access private key material, with an emphasis on maintaining individual sovereignty and providing simple off-ramps to self custody.
First, some initial definitions of key terms:
Wallet: the interface for signing transactions
Key: the private material that authorizes transactions
Blockchain address: an onchain “account number”
Understanding Digital Ownership
In the early days of digital ownership, the above objects have been highly intertwined. Specifically, one key was associated with one blockchain address often accessed through a wallet that also stored the key (aka an EOA).
It’s important to note that the term “digital ownership” is different in some ways from traditional legal ownership, as exemplified by the popular adage “Not Your Keys, Not Your Crypto”. Using this as guidance, the only way to own digital goods is to own your underlying key(s) with self-custody.
Self-custody, or managing your own keys, is a sophisticated and serious task. Self-custody is deeply empowering to individuals since they take on the full responsibility of key management and assume complete control over their digital assets. Taking on this responsibility can be complex and cumbersome, especially for people who are new to web3 and the notion of digital ownership, since keeping a secret safe requires care and attention.
In the first decade of digital ownership, there has been another popular option for managing digital goods: the centralized custodian. Centralized custodians are companies (often taking the form of a cryptocurrency exchange) who hold keys on behalf of their users. This makes the custodian the sole owner of the digital assets and allows them to set rules about what can be done with these assets (which is often restricted to trading on the exchanges they run). Essentially, the deal here is that the custodian provides their customer with legal ownership over these assets, as well as an easy way to manage them with “web2 style” sign up. This has ended poorly before, to say the least.
This presents an exciting challenge: how can digital ownership catch on if the easiest way to start participatingwith digital ownership is to actually give up this ownership to a custodian?
Blockchain Virtual Machines and Account Abstraction
In order to explore this question thoroughly, let us dive into a bit more background. First, a virtual machine is a software program that creates a virtual computer that runs on a physical computer. The Ethereum Virtual Machine is a non-traditional virtual machine since it runs programs distributed across all of the nodes in a given network. Initially, these EVM programs were used for executing the logic of applications, called smart contract dApps. Now, verification logic has been introduced on the EVM to individual users’ wallets, so let’s introduce another definition:
Smart Contract Wallet: A programmable blockchain address account
One of the most exciting features that can now be programmed into blockchain addresses is called Account Abstraction (AA). Prior to this, blockchain addresses and keys were functionally the same thing for individuals aka Externally Owned Accounts (EOA). With Account Abstraction, individuals can now have one or more keys associated with their blockchain address.
Decoding Key Management
With this background established, let’s move into defining key management as a category. Key management refers to where the key itself is stored. As introduced above, this may be an EOA (key lives with the user), a custodian (key lives with the exchange or centralized party), or methods for distributing keys into shares, which is explored below.
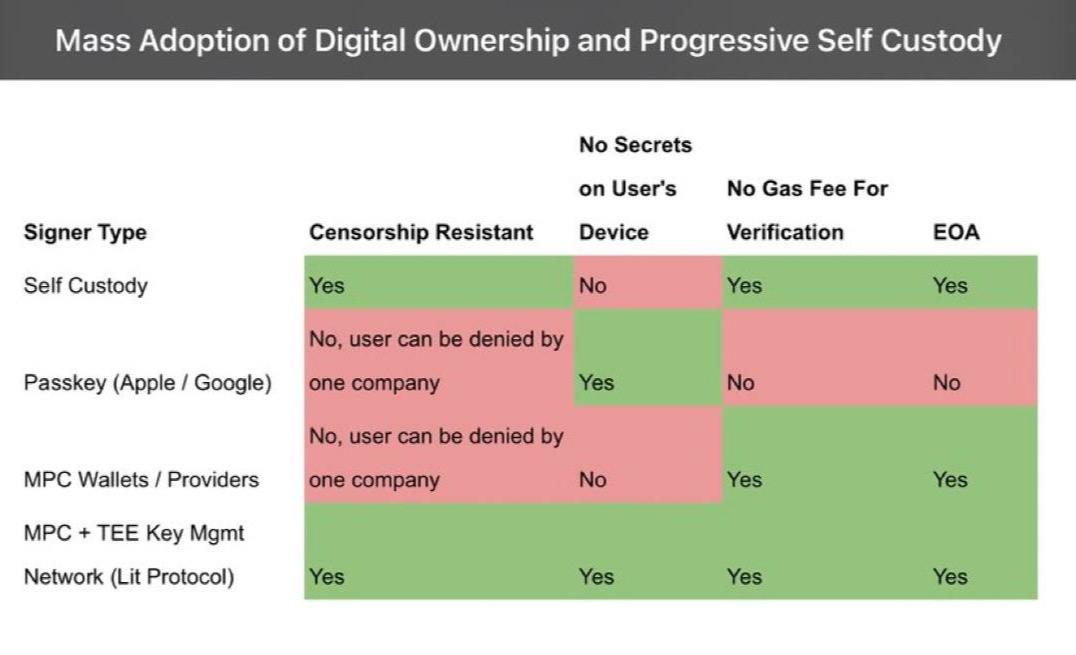
Theoretically, any key can work with AA. Additionally, with AA there can be more than one valid key and / or more than one key required to use the account. With AA, the key is often called a ‘signer’ so let’s take a look at the different types of signers and their attributes:
Self Custody works the same way as defined above, the key is an individual's responsibility.
Passkeys are a product offered by Apple and Google that allow for an application specific key to be stored in the cloud keychain of the provider (e.g. iCloud). Given that it requires more computation, there is a gas fee associated with validating a signature from a Passkey in an EVM / with a blockchain. Additionally, passkeys are not EOA keys and therefore don’t function in the modular and multichain blockchain without broad adoption and implementation of standards across blockchains and smart contract apps.
MPC stands for ‘multiparty computation’ and is a technique typically used in conjunction with Threshold Secret Sharing (TSS), a method for storing a private key in multiple parts (often referred to as ‘shares’). These systems are often defined as “x of n” MPC, where n is the total number of parts a given key has been broken up into and x is the number of shares required to authorize a signature using this distributed key. It’s worth calling to mind that MPC is just a technology and like the use of every tool, it can be welded and implemented in various ways.
MPC Wallets / Providers follow a few different implementations. The most common is 2 of 2 where the key is broken up into two parts and one is self-custodied by the user and the other is held by a company. With MPC providers, funds can not be stolen and used by the company, but these companies are also a reliant party given that authorization from their key share is required for any transaction. In other words, these companies and their users dually own the digital goods, with neither party being able to anything without the other.
MPC + TEE Key Mgmt Network is the distributed key management system that the team behind Lit Protocol is building. At launch, Lit will be a 20 of 30 MPC network with a growing number of nodes and support for a variety of authentication methods. In this network, each node operator runs the protocol inside of a Trusted Execution Environment (TEE). With the current state of cryptography, the inclusion of the TEE in any MPC network is vital since key shares cannot be revoked. Today, Lit supports AMD’s SEV-SNP as a TEE, which is the private processor that underpins the confidential compute offerings from Google, AWS, and Azurse for their banking and enterprise customers.
Lit has been built with the following goal in mind: to provide developers and users with the most self-sovereign way to access private key material for signing and encryption, without requiring any trade offs in UX.
Progressive Self-Custody: A User's Journey
With all of this covered, let’s chart out a user flow for progressive self custody using Account Abstraction and Lit:
Alice has heard about web3 and wants to buy an NFT. She’s sitting at her laptop, navigates to a marketplace, and then clicks “Sign Up”.
A window pops up and props Alice to sign in with Email, Google, or Apple. In this case, Alice selects Google and proceeds through that sign in flow.
In the background, a smart contact account is created with a Lit Programmable Key Pair (“PKP”) used as the signer. This PKP is set up with Alice’s Google account being used as the authentication method.
Alice is now signed in and she’s in the mood to buy an NFT so she funds her wallet with $20 USDC via a fiat onramp. Just at that moment, she realizes the time and has to run out the door to make the train. After Alice boards the train, she uses her phone to navigate back to the marketplace. Once there, she clicks ‘sign-in’, using the same Google account as before.
In the background, the nodes of the Lit network have validated her Google oAuth credential inside of the TEE, provisioning the key shares to Alice and allowing her to sign a message from her PKP and authorizing her to connect her AA wallet to the marketplace.
Alice then sees a cool NFT that just dropped and buys it. Luckily for Alice, the AA wallet also has a paymaster and Alice can pay for the gas in USDC.
She thinks this NFT is awesome and knows that she has a friend who had their Google account stolen so she decides to add her phone number as a secondary auth method on her PKP.
It turns out Alice has a good eye and over the next few days the price for her NFT skyrockets. She gets a notification from her wallet about this and decides she wants to add more signers to her AA wallet. She is a lifelong Apple user and adds her iCloud Passkey as signer, which acts as the backup for the PKP, which is currently using her Google Account with SMS for two factor authentication.
A few months go by and Alice has the time to read all about crypto and decides that self-custody is right for her. She adds a key stored in a hardware device as a signer on her AA wallet and removes the Lit PKP and the Passkey as signers.
What makes this a highly favorable route for mass adoption is that Alice created an account in the same way she would sign up for any web app, without giving up having to trust one company to store any private key material and also without her having to store any secrets herself.
Conclusion: The Future of Digital Ownership
Progressive self-custody presents a promising solution to the challenges of mass adoption of digital ownership. By allowing individuals to take control of their digital assets step-by-step, with the starting step of an MPC + TEE network like Lit, more people can participate in the digital economy, without compromising security or ease of use leading to a more individually empowered tomorrow. If you’re working on Smart Contract Wallets and want to explore and see how we can collaborate, please get in touch on Twitter or Discord! Let’s Free The Web.

